Analytics Automation
Uncover hidden insights—without digging through data
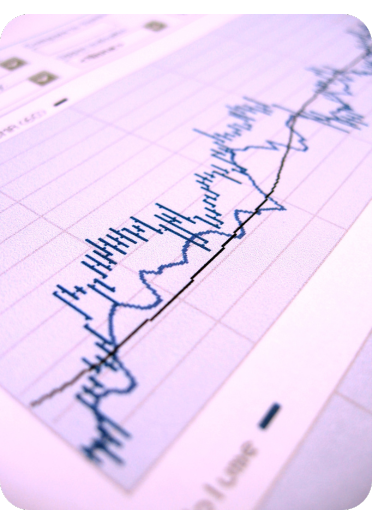
Real-time dashboards
Connect all your data sources in one unified view
AI powered analytics
Get questions answered instantly, no reports needed
AI recommendations
Receive personalized solutions you didn’t know you needed
Scheduled reports
Get the reports you need, delivered automatically
Insight alerts
Get notified of changes, before they become problems
Frequently asked questions
How does the process work?
We follow a proven, structured process that's both simple and effective, ensuring we align with your goals and deliver the best possible results every time.
- Consultation: We'll discuss your goals and develop a tailored automation strategy.
- Development: We'll design, build, and test your automation solution.
- Support: We provide training, documentation, and ongoing support to ensure success.
How long does it take to develop one solution?
Developing one automation solution can take anywhere from a few hours to a couple of weeks, depending on complexity and the number of steps involved. Contact us or schedule a chat for a more accurate timeline for your project.
Do you offer training or resources to help us manage the automation?
Yes, we provide individual or group training, solution documentation, explainer videos, and ongoing support to ensure you’re fully equipped and supported after implementation.
Can you automate custom processes unique to my business?
Of course! That's our specialty.
What makes your automation solutions different from others?
The difference is in the details. Even the simplest automation solutions deserve expert craftsmanship and attention to detail. Whether it's built-in error prevention and handling, intuitive management, or inherent flexibility, our team ensures solutions that are robust, scalable and future-proof.
Is my business data secure?
Absolutely. We prioritize the security and confidentiality of your data. All of our systems are built with robust encryption, secure access protocols, and compliance with industry best practices to safeguard your sensitive information.
%20smaller.png?width=591&height=140&name=logo%20(1)%20smaller.png)